Best DAST Tool: Runtime Security For Mobile Applications
- Bugsmirror Research Private Limited

- Feb 16
- 3 min read
Dynamic application security testing (DAST) tools are designed to identify runtime security vulnerabilities in mobile applications. These tools test applications from the outside, simulating real-time attacks like an attacker would. These tools analyse live application behaviour and runtime interactions to uncover exploitable weaknesses.
Today, over 90 per cent of the population uses a mobile phone, and most fintech companies rely heavily on mobile apps that process billions of user interactions, transactions, and data transfers every day. This scale makes mobile apps a prime target for attackers seeking to exploit vulnerabilities to steal data, gain unauthorised access, and launch other security threats. Dynamic Application Security Testing (DAST) tools play a critical role in identifying these risks and help organisations assess their app security in live environments.
What are DAST Tools?
DAST tools are runtime security testing tools that identify runtime threats in mobile apps as they run on a device. This assesses an app’s security strength and reveals how attackers can exploit vulnerabilities during execution. By exposing these attacks, DAST tools help teams strengthen application security to protect their apps from abuse in live environments.
Key features:
It detects real-world attacks, such as code injection, cross-site scripting, app tampering, etc.
Tests the application security without accessing the source code.
It is also called Black-box testing, where the application is tested as an external attacker.
It's automated testing.
It gives low or no false positives.
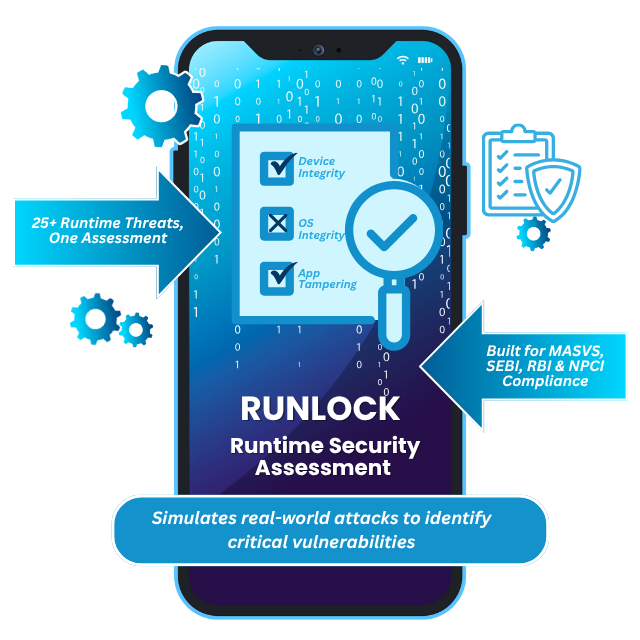
Bugsmirror RunLock: A runtime-focused DAST solution
Bugsmirror RunLock is an advanced dynamic application security testing tool that offers runtime vulnerability detection in Android and iOS mobile applications by running apps on real physical devices. RunLock is known for assessing over 30 runtime threats. This is an automated tool that provides results within 24 hours, making the testing and deployment process easier and less time-consuming.
How Bugsmirror RunLock works:
Bugsmirror RunLock is an automated tool; it just requires an APK file or ipa file. It tests the app against different runtime threats, identifies security bypasses, and provides a report within a few hours, which makes it very time-efficient and with no false positives.
It detects a set of measures threats, including:
Feature | Description |
Device Integrity | Detect device compromise indicators like Jailbreak, emulators, and cheat tool use. |
App Tampering | Identify repackaging, code modification, and unauthorised changes to app structure. |
OS Integrity | Check for alterations in OS-level components that compromise your app's security. |
Secure Communication | Validate communication layer protections, e.g., SSL pinning and packet sniffing checks. |
Mobile Privacy | Test your app’s protection against insecure screen capturing and mirroring. |
Mobile Fraud | Detect fraud scenarios, such as App Cloning/ Second Space Prevention, Keylogger Prevention, and Time Manipulation. |
Social Engineering | Validate if your app is downloaded only from a trusted app store. |
Why Choose RunLock:
Threat severity level (high/medium/low) to take measured actions.
Give the report in 24 hours.
CVSS risk scores (Common Vulnerability Scoring System).
Government guidelines and industry standard-aligned categories (including RBI, NPCI, OWASP MASVS, etc).
Attempts are made to bypass existing app security measures. Pass/fail/bypassed results.
Make it easier for developers to fix issues, for leaders to understand risk, and for compliance teams to use the findings for audits.
Runtime DAST is especially important for fintech and high-scale applications because:
One bypass can expose millions of users.
It can lead to financial fraud or data leakage.
Security failures occur post-release, not only during development.
Compliance does not guarantee resilience against real attackers.
FAQs:
Which is better, SAST or DAST?
Ans: SAST and DAST tools are both needed to secure applications effectively. SAST finds vulnerabilities in the code in the app development stage, while DAST identifies runtime risks when the application is running on a device. Together, they provide complete application security coverage.
Is DAST expensive?
Ans: DAST does not have to be expensive. Modern DAST tools offer automated, scalable testing that reduces manual effort and long-term security costs caused by breaches.
Is DAST still necessary?
Ans: Yes, DAST is still necessary because many vulnerabilities only appear when an application is running. It helps detect runtime issues, misconfigurations, and attack paths that static testing cannot find.
Conclusion
Dynamic application security testing is only effective when it reflects real attack behaviour. RunLock delivers true runtime DAST by testing mobile apps on real devices, simulating advanced attacker techniques, and exposing whether security controls can actually be bypassed.
If you want to understand how strong your mobile app security really is, not just what’s configured on paper, Bugsmirror RunLock provides the visibility that matters.
Get a free audit of runLock and validate your runtime security at your email within 24 hours.



Comments